Staff scheduling integrated with invoicing and customized reporting.
QR enabled patrolling (geo-fencing) with real-time updates.
Accuracy and transparency of incident reporting on the spot.
Reducing paperwork and minimizing human errors.
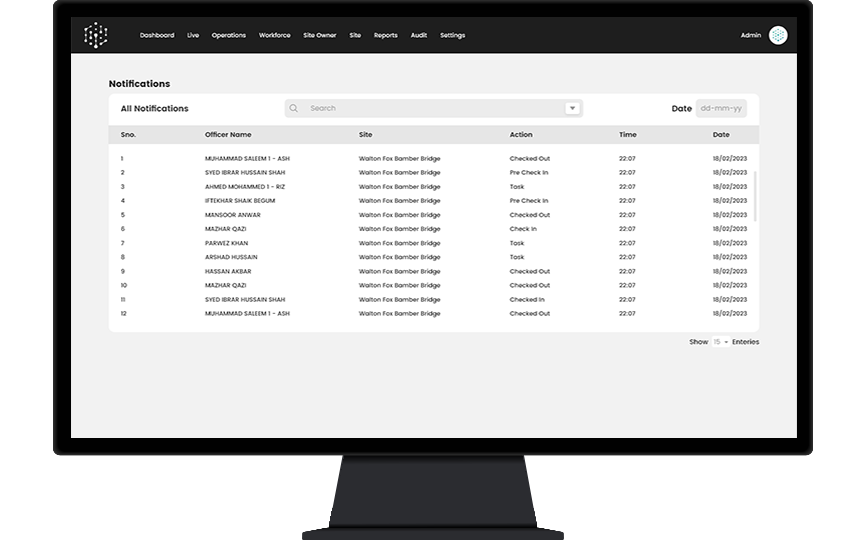
Live tracking and push notification means no need to constantly call the staff.
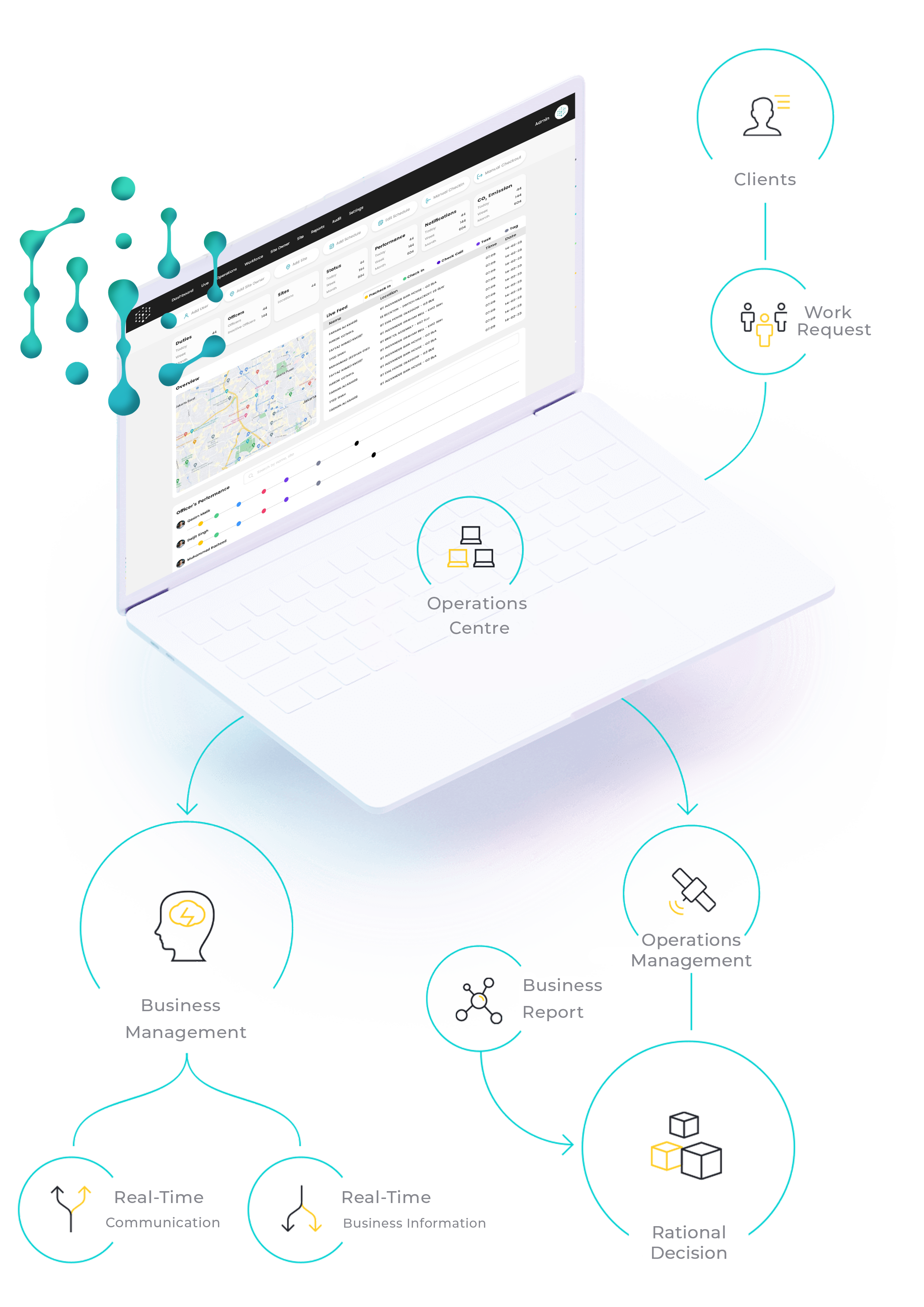
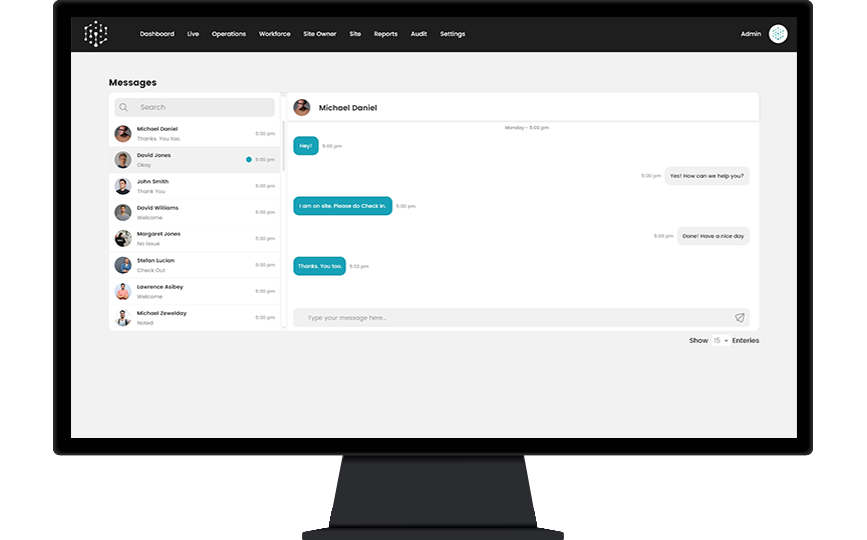
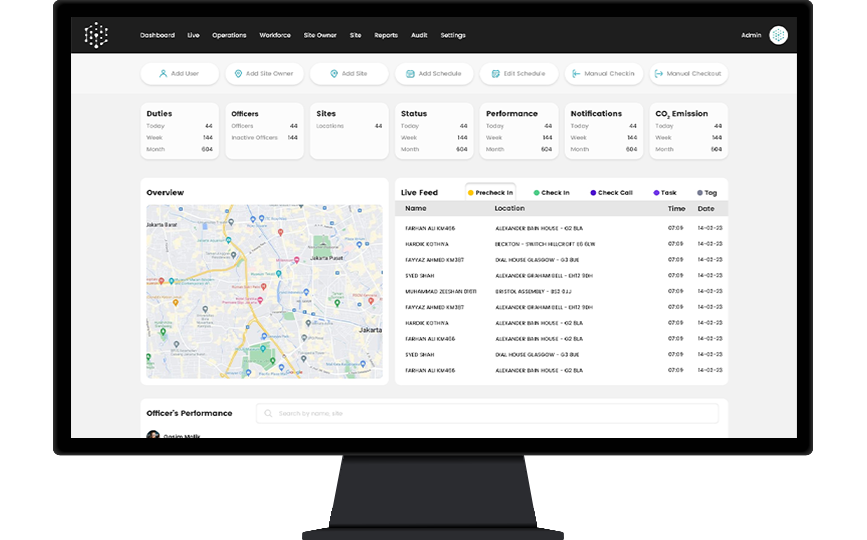
Vigilink’s cloud-based solution manages the flow of information from clients, contractors and others through the Operations Centre and disseminates it to different stakeholders with complete traceability and transparency. This enables you to make informed business decisions based on real-time information to increase your profitability.
All data stored on your online server for instant access & usage.
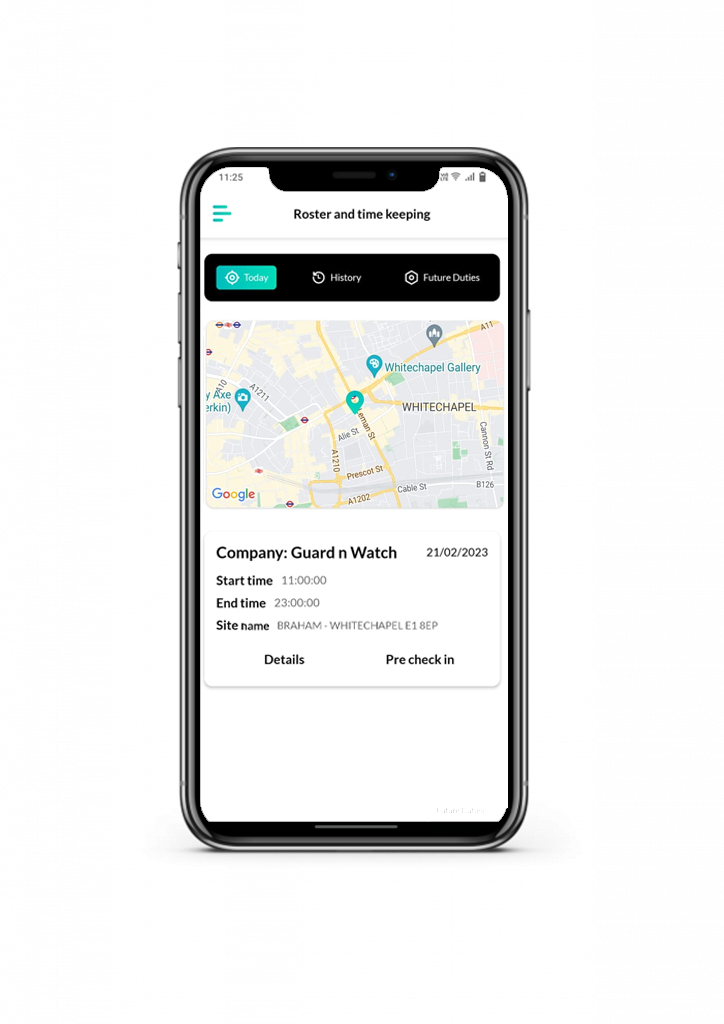
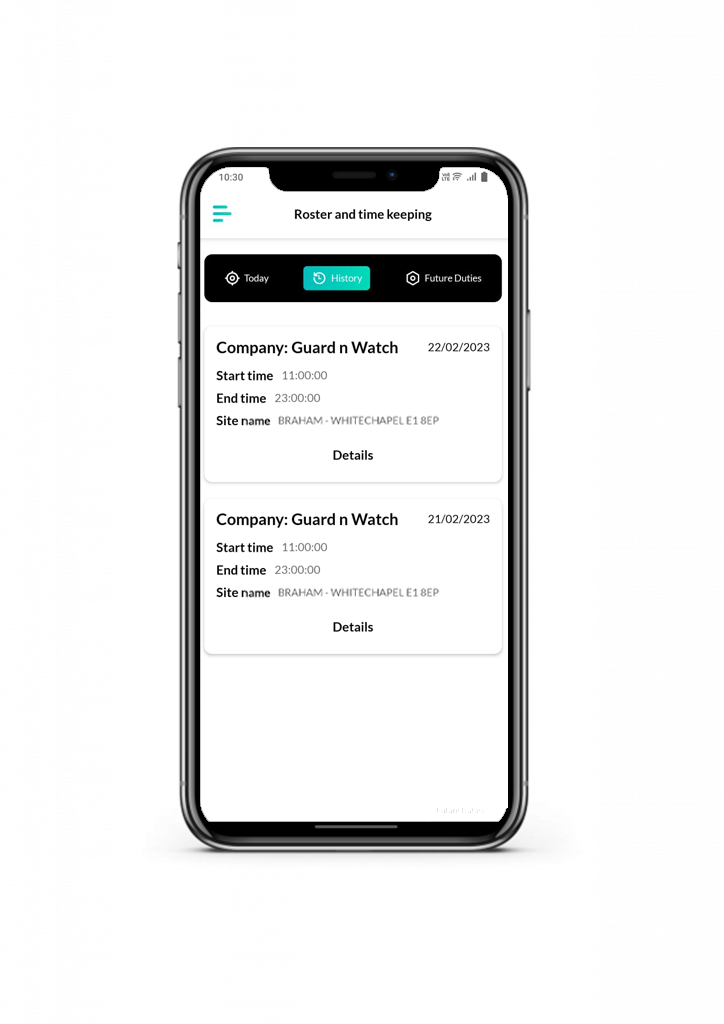
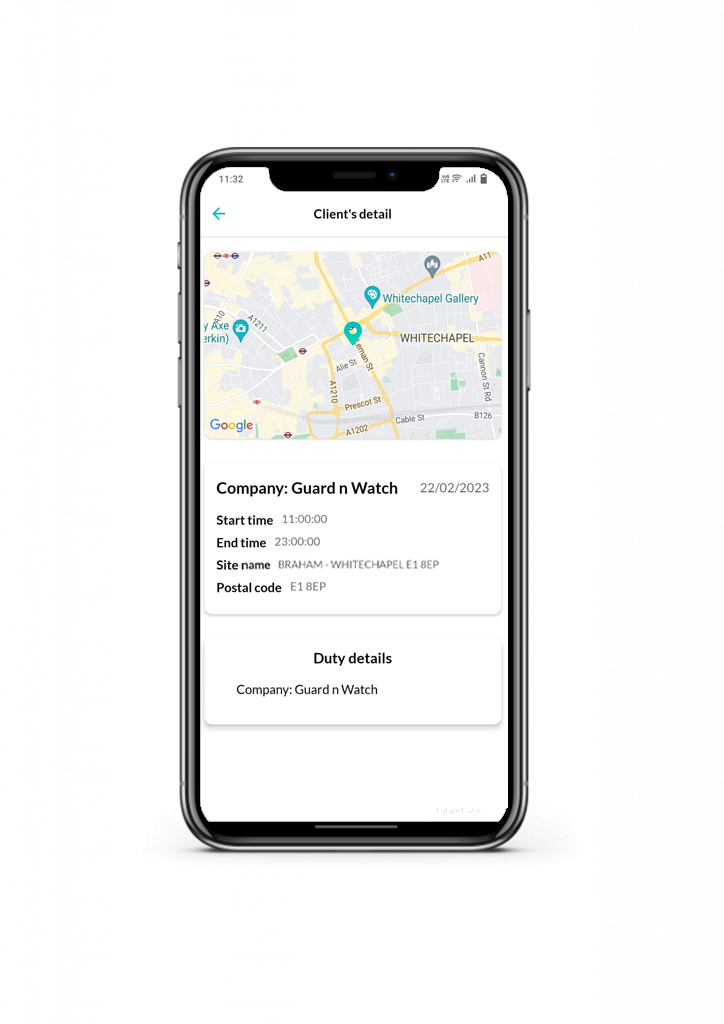
Detailed information of your business at the palm of your hand.
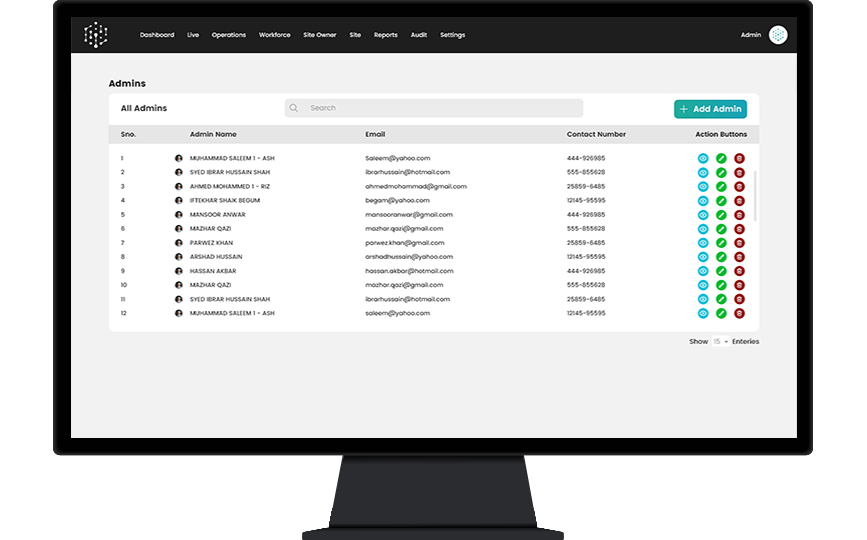
Only authorized access allowed.
We have a team of certified experts who’ve got you covered.
We have an online support system working 24/7.
Improve productivity by automating routine tasks, streamlining processes, and optimizing work schedules.
Save money by reducing labor costs, minimizing employee turnover, and increasing overall productivity.
Plan your workforce more effectively by providing insights into workforce trends and patterns.
Help improve employee engagement by providing employees with more control over their work schedules.
Comply with labor laws and regulations by ensuring that employees are working within legal limits.
Database
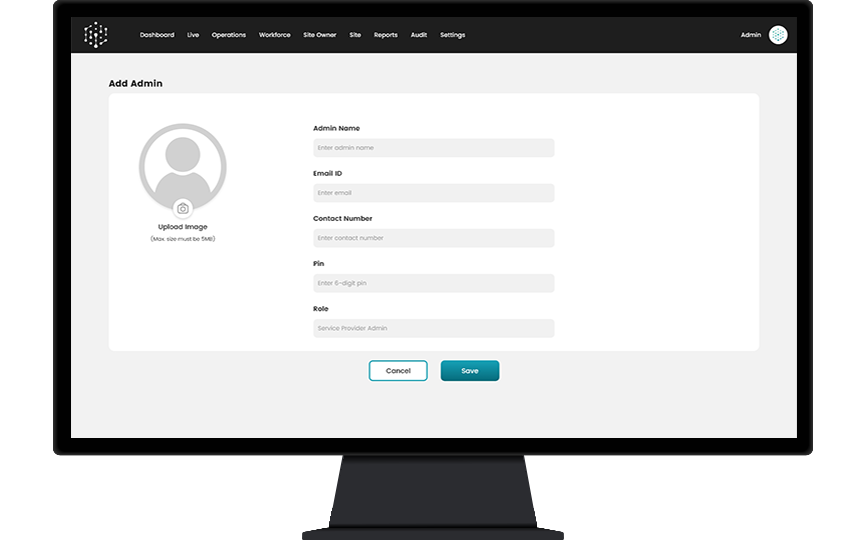
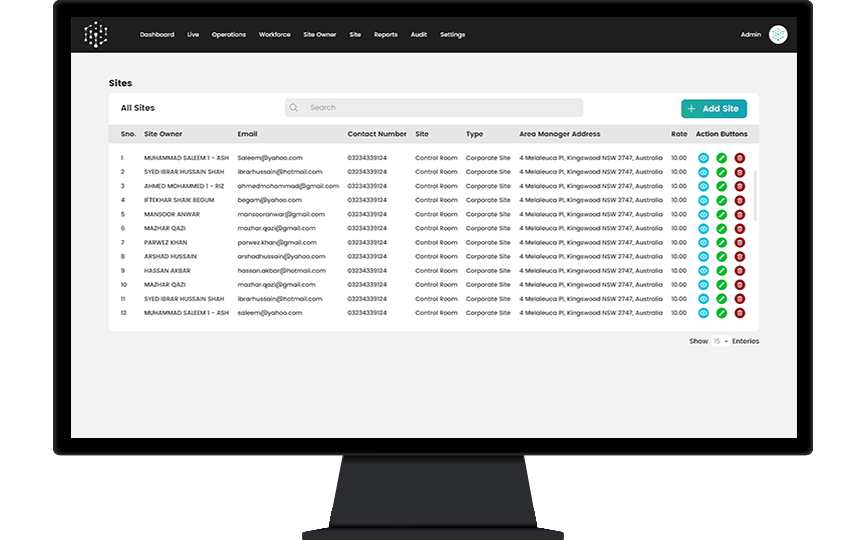
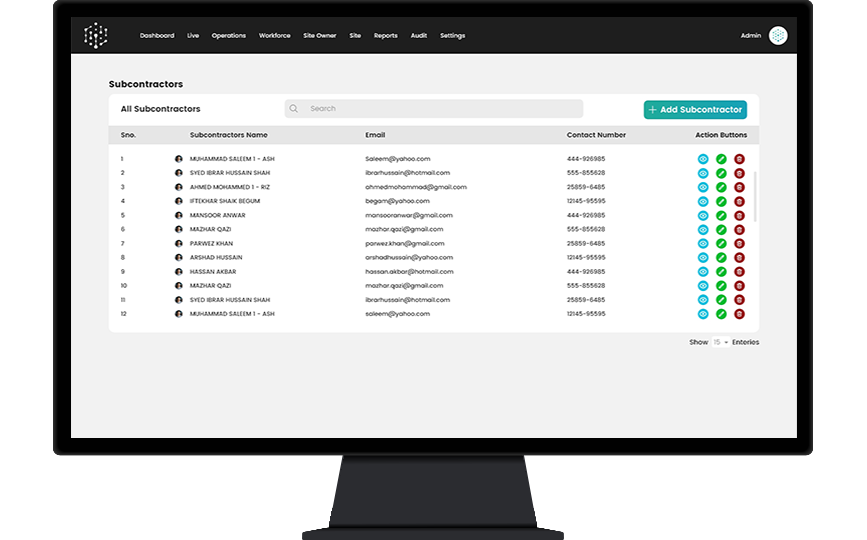
Vigilink allows you to build Quality Management & Robust System complaint database for your staff, clients, incidents, accidents, site visits, duty records and operations.
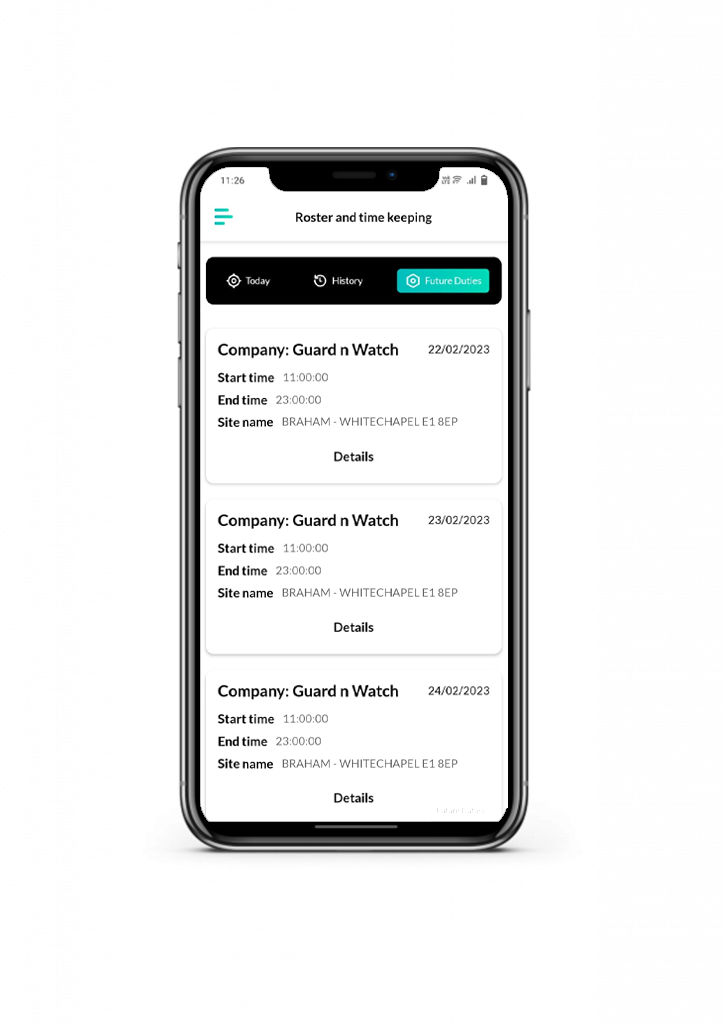
Scheduling
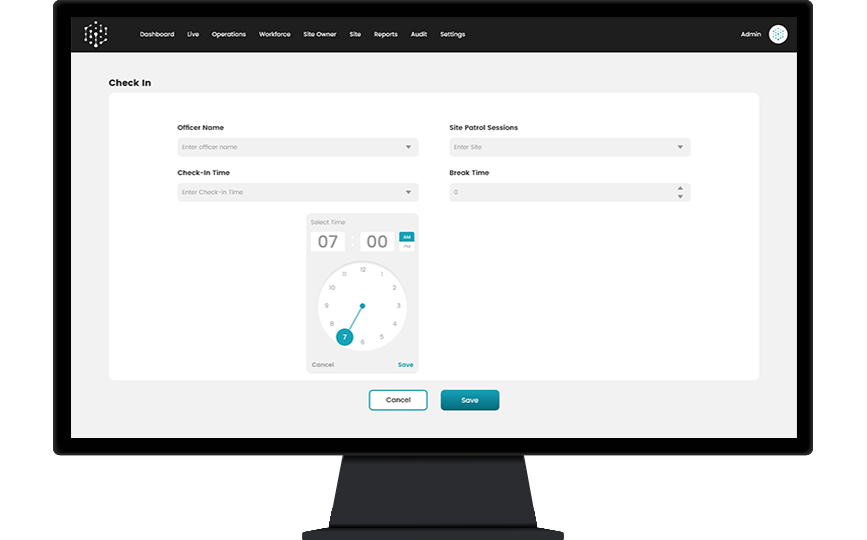
Automate the scheduling, management, reporting and analyses of staff shifts using real-time data intelligence and analytics to optimize operations and improve profitability.
Tracking
Improve the speed, accuracy and transparency of incident reporting by leveraging live-tracking capability and by enabling the duty guards to directly report on the incident.
Carbon Footprints
Inventory & Task
Achieve a better work-life balance and a peace of mind while our software solution automates your tedious manual tasks to free up your time.
Patrolling
Increase the reliability of your service operations by issuing alerts and notifications to confirm shifts along with guard tour, in-shift patrol and checkpoint scans, data available to all relevant stakeholders.
Incident Alerts
Improve the speed, accuracy and transparency of incident reporting by leveraging live-tracking capability and by enabling the duty guards to directly report on the incident Management System.
Reports & Audits
Automating and efficiently integrating the business operations database through the software platform along with real-time audit reporting.
SECURITY
CLEANING
HEALTHCARE
PHONE: +44 333-567-0566
wHATSAPP: +971 56-692-0566
SATURDAY: 11:00 – 17:00
Digital World Center, 1 lowry plaza, The Quays salford Manchester